
Safe browsers for secure safety and privacy online are important because they keep your personal information and browsing history private.
They also protect you from malicious websites that could harm your computer.
Some safe browsers include Firefox, Chrome, and Opera. Many people use these browsers because they are fast, reliable, and secure.
For years, Firefox has been a leader in privacy and security features. If you are looking for a safe and private browser, consider using one of the browsers listed below.
They are all reliable and provide excellent security features. Be sure to keep your computer protected with antivirus software and a firewall, and be careful about the websites you visit.

You are incredibly vulnerable to hackers if you do not use a private web browser or a virtual private network to protect your regular internet connection (VPN). All of your ideas, images, text, and so on are ready for those in charge of your internet access.
Many browsers have private modes that delete cookies, browsing history, and cached files when you close the window. You can also use a secure browser extension like HTTPS Everywhere to ensure that your connection is always encrypted.

These steps are essential for journalists, activists, and others who need to keep their work and communications safe from prying eyes. In addition to using a private web browser, you should also use a Virtual Private Network (VPN).
A VPN creates an encrypted tunnel between your computer and a server somewhere else on the internet. This protects all of your traffic from being monitored or intercepted by someone else.
You are defenseless when using the internet because your computer's security is all you have. This is especially true for inquisitive children who are always looking for a new web-based adventure.
While you, as a responsible adult, are aware of the concept of a virtual private network, your children are not. To keep your children safe online, you must teach them internet safety.
If you don't have children, it's still important to use a secure browser because your personal information is at risk. You can never be too careful when it comes to your privacy.
Anyone who has access to your computer should report potentially dangerous websites. You should be able to disable tracking in the best browsers. Malware includes rootkits, keyloggers, DoS attacks, and flaw exploits.
Hackers can use them to gather data and exploit your position. You should also use a password manager and two-factor authentication.

Many browsers offer these features, and they can help keep you safe. There are a number of different browsers available on the market, and each one has its own advantages and disadvantages.
Some browsers are more secure than others, and it is important to choose the right one for your needs. In general, the most secure browsers are those that offer strong security features such as tracking prevention, malware protection, and password management.
The most secure browser (if you utilize all of its features) is Tor. However, Brave is better suited for those not so technologically advanced.
If you're looking for a more secure browsing experience, one way to achieve this is by using a private web browser.
Private browsers help keep your information and activities confidential and can be useful for online banking, shopping, and other activities that you may want to keep private.

There are many different private browsers available, but some of the most popular ones include Tor Browser, Brave Browser, and Firefox Focus.
Each of these browsers has its own unique features, so be sure to read up on them before deciding which is best for you.
One important thing to remember when using a private browser is that it's important to keep your software up-to-date.
Brave, Iridium, and WaterFox are all top-rated private browsers that keep your browsing data to yourself.
Brave is a Chromium-based browser with built-in ad and tracker blocking. Brave also rewards you with BAT tokens for viewing ads.
Iridium is a secure, privacy-focused browser that encrypts all traffic with TLS 1.3 and offers a host of other security features.
WaterFox is a Firefox-based browser made specifically for 64-bit systems. It’s highly customizable and includes many privacy features.
All of these browsers are available for Windows, Mac, and Linux. They can be downloaded from their respective websites or from the app stores on your device. Give them a try and see which one works best for you.
All of these browsers are available for Windows, Mac, and Linux. They can be downloaded from their respective websites or from the app stores on your device. Give them a try and see which one works best for you.
The most popular browsers, including Google Chrome, Mozilla Firefox, Apple Safari, and Microsoft Edge, have security issues.
These browsers have features that appeal to a wide range of users. These features, unfortunately, rely on users providing personal information, which is then used to tailor and personalize the user experience.
You may not be aware that safe browsers are available for download, but they are not widely used because they do not personalize the user experience.
The following are the most secure internet browsers:
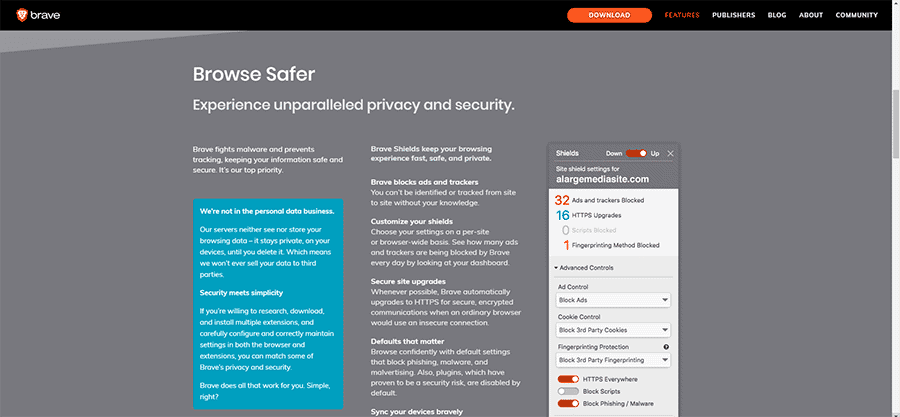
According to Brave Software Inc, it is based on Chromium but has many vulnerable features removed. It is concerned about privacy. It doesn't keep track of who's using it or what they're looking at.
Trackers and ads are blocked by default, and plugins are disabled. It has a built-in script blocker and prevents browser fingerprinting.
When it's in use, it switches to HTTPS. All of these security measures result in a faster browsing experience.

Iridium is a browser-based on a stripped-down version of Chromium that incorporates several improvements that result in extremely tight security.
Users can look at the Git repository to see what has changed in each build. It's simple to use and can be installed on a corporate network.
It's another quick browser because it's stripped down for safety and security.

Waterfox is a web browser with a Git repository based on a Firefox fork. Users can view the changes in the Waterfox code through Git for their peace of mind.
WaterFox, unlike Firefox, does not collect user data or track browsing history.
If you're looking for a fast and private browsing experience, Waterfox is a great choice.
The tor browser, which is based on the Tor network, employs numerous connections and encryption as part of its normal functions. These characteristics, to the greatest extent possible, ensure users' security and privacy via the Tor network.
Tails, on the other hand, is limited by the use of the Tor network and its underlying technology. As a result, it has sluggish speeds, faulty exit nodes, and connections to US authorities and other security vulnerabilities.
You may use the Tor browser, but you'll need to connect it with a VPN and turn off the Tor network for security reasons.
Changing the preferences, on the other hand, might result in Tor browser problems. As a result, using the Tor browser may not be worth the effort in the end.
Why should newcomers use a VPN? A VPN should use strong encryption to protect your online privacy. Cybercriminals are always looking for new exploits.
However, interactivity and compatibility are threats to all devices and platforms. Android users can use a VPN app to protect themselves while using their phones. A VPN app protects and secures your computer online, just like at home or work.
Many people use a VPN to keep their browsing history and activities private. Both a VPN and a secure browser are essential for safe online browsing. You should use them whenever you're going online, whether you're at home or traveling abroad.
The internet is a dangerous place. It’s full of hackers and fraudsters who can steal your bank details, passwords, or even break into your computer.
And because it’s so easy to hide their tracks on the internet, you might not even know if someone has gotten into your accounts until long after the damage is done.
But there are ways for you to protect yourself from these threats and make sure that none of them ever get close enough to do any harm: Secure browsers are one way to do this!
